5 Information Security Mistakes To Be Aware Of
For many, information security mistakes are a fact of modern life. As devices proliferate and technology works it’s way into our lives in every way, information security becomes a growing concern. Through this blog post we discuss 5 common information security mistakes and how you can protect yourself in the future.
Information Security Breaches Are Alarmingly Common
A security breach is a security incident in which sensitive, protected or confidential data is copied, transmitted, viewed, stolen or used by an individual unauthorized to do so. Security breaches/ hacks/ social engineering – regardless of what you call it, these attacks are on the rise, now 44% of small businesses and 48% of enterprises admit to being a victim to a security breach. You can do your best to attempt to make your systems secure, but it’s impossible to prepare for absolutely everything, as the attacks are becoming more sophisticated. According to a Verizon Data Breach report, 85 percent of organizations breached did not realize they had been compromised for weeks or longer, and they usually only found out after an external third party alerted them. The Wall Street Journal reported that cybercriminals had access to Nortel Networks corporate network for nearly a decade before they were discovered.
Regardless of the type or size of the security breach, they can be expensive – the average cost of an attack can be anywhere between close to $9,000 for a small business to upwards of $100,000 for enterprises per security incident. What’s more, add downtime to the equation and the cost skyrockets exponentially. Downtime can be costly.
Average Downtown Due to a Information Security Breach
- Less than 1 day – 38%
- 1-3 days – 40%
- 3-7 days – 11%
- More than a week – 7%
- More than two weeks – 5%
- Source: NSBA
Who is responsible for these attacks and what is the motive? Surprisingly, most of these attacks are avoidable. What information security mistakes are your company making – that you may not be aware of?
1. Company Failure to Identify Employees as Threats
80 percent of security breaches are crimes of opportunity and surprisingly the largest security threat is employees.
Why are your employees a risk?
Lack of Training
It’s important that employees know how to recognize phishing emails, fake websites, social media risks and Trojan downloads. Regular training at hiring orientation as well as review time is critical to train employees on cyber security best practices. It’s also important to offer ongoing support. Possible culprits include:
- Employees opening attachments from unknown sources and may contain a virus
- Employees visiting websites that they shouldn’t
- Employees providing confidential login information via phishing emails
Employees’ Lack of Awareness
Unattended computers is one of the main reasons. Trend Micro reports that 77 % of employees leave their computers unattended. Unattended computers can lead to compromising confidential information.
Disgruntled Employees
FBI Cyber Investigations revealed that between 5,000-3 million dollars is lost a year due to cyber incidents by disgruntled employees. This is something that is hard to plan for, as you really have no idea how your employees will react to organizational changes – for example, lay-offs; that’s why it is a good idea to always be prepared. Learn from these companies to not underestimate the power of a disgruntled employee.
- Terry Childs, a former network administrator for the City of San Francisco, held the city’s systems hostage for a time. He refused to surrender passwords because he felt his supervisors were incompetent. Childs was convicted of violating California’s computer crime laws in April 2010.
- In June 2012, Ricky Joe Mitchell, a former network engineer for oil and gas company EnerVest, was sentenced to prison for sabotaging the company’s systems. He found out he was going to be fired and decided to reset the company’s servers to their original factory settings.
- It was discovered in 2007 that database administrator William Sullivan had stolen 3.2 million customer records including credit card, banking and personal information from Fidelity National Information Services. Sullivan agreed to plead guilty to federal fraud charges and was sentenced to four years and nine months in prison and ordered to pay a $3.2 million fine

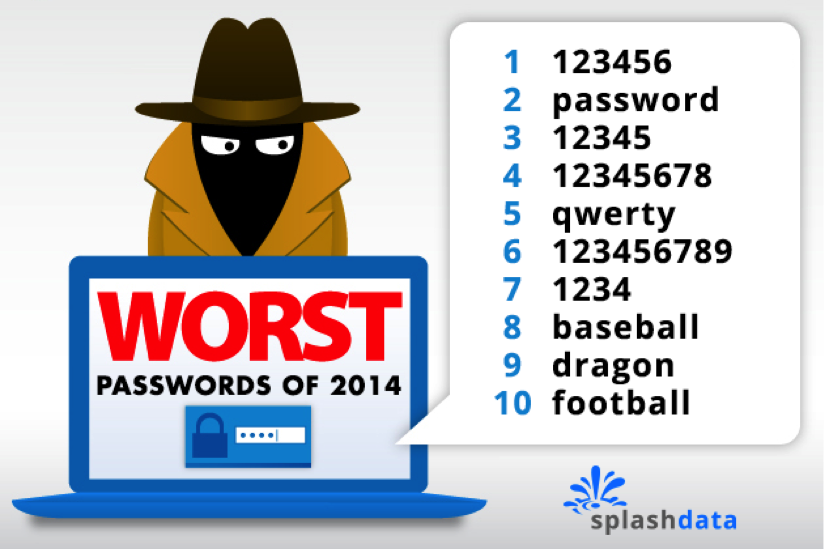
2. Allowing Weak Credentials (Passwords)
According to data breach investigations report by Verizon, weak or stolen login credentials is the most common information security mistake. Approximately 76 percent of attacks on corporate networks involved weak passwords. In addition, another 48 percent of hacking breaches involved stolen passwords gained through malware, phishing attacks or the theft of password lists. Such authentication information provides a vulnerable point that can be easily exploited by hackers. Weak passwords allow hackers to gain access to your system and can possibly gain access to your entire organization.
Credential and password culprits include:
- Re-using old passwords
- Using default passwords
- Sharing passwords – i.e.: asking co-workers to log in for you during vacation
- Not regularly changing passwords
- Using non-sophisticated passwords
Make sure that you integrate a password policy in your organization. Some good password best practices include:
- Ensure that remote access passwords and passwords for systems aren’t default passwords. If a third party handles this for you, make sure you confirm that they aren’t using a default or the same password as with other customers.
- Use two –factors to authenticate users – i.e.: a strong password as well as a security question.
- Password history policy – This stores several previous passwords so that the user can’t use the same password when it expires.
- Define minimum and maximum password age – Passwords can’t be changed until they are more than a certain number of days old and the passwords expire every 30-90 days. Long passwords–seven or more characters–are usually stronger than short ones.
- Implement a “password must meet complexity requirements” policy setting. This policy setting checks all new passwords to ensure that they meet basic strong password requirements. For example, passwords much contain upper and lowercase letters, numbers and symbols.
- Create a password policy; passwords must follow:
- Upper and lowercase letters, numbers and symbols.
- Use a separate password for each registered site
- Password protocol that will force employees to change their password every 30-60 days and ensure that weak passwords aren’t permitted. A password management system can help by automating this process and eliminating the need for staff to remember multiple passwords.
- Online accounts are updated immediately upon an employee’s dismissal.
- Avoid using any passwords from SplashData’s Annual Worst Passwords List.
3. Weak or Non-Existent Information Security Policies
It’s important to have a comprehensive information security plan(s) in place to ensure that management and IT are on the same page. Security and business goals should be aligned so security issues are seen as a corporate problem and not just an IT issue. It’s important that when IT makes decisions that they consider how their projects will impact the overall business goals. Some important policies include:
Security Policy
How is new data added and classified? How are people given access, and how often is that access reviewed? Are the backups and redundancies sufficient for the type of data? How is data access monitored and reported on? Is sufficient data loss prevention in place to protect the company? And, once the data reaches its end-of-life, how is the data disposed?
Laptop Policy
Stolen laptops are a common problem that can contribute to security breaches. A laptop policy will help ensure that employees aren’t leaving their laptops unattended or even left in their cars. Organizations should also log all corporate devices that employees have and deactivate any of terminated employees.
Research shows that 56% of employees very frequently or frequently stored sensitive data on their laptops, smartphones, tablets, and other mobile devices.
Social Media Policy
Establish a policy to outline how employees are allowed to use social media and consequences for not conforming to it. A social media policy should also include what employees are allowed to post on behalf of the company. Your social media policy should extend to your corporate devices as well, as some social media site apps contain malware and can steal company information on a device.
Snapchat was hacked and the information of 4.6 million users was leaked. If a corporate device connected to a company’s network had become infected, that malware may spread to the rest of the business.
Company Equipment Disposal Policy
Not disposing of data correctly, for instance, donating computers that still contain data on them can expose confidential data. A policy that ensures that files are permanently deleted prior to donating or throwing out old computers and devices can help.
4. Using Weak Encryption
Encryption is the process of encoding messages or information in such a way that only authorized parties can read; using weak encryption can open companies up to attacks and compromise intellectual property or personal information, as well as other security vulnerabilities. What are some of the causes?
- Emailing unencrypted data
- Having unencrypted data on mobile phones
- Allowing employees to take sensitive data home on work computers
- Data in transit
- Employees working remotely
- Companies may use weak encryption keys
- Easy to use pass phrases
- Emailing passwords and pass phrases to co-workers
- Using proprietary encryption
- Failure to use two layers of encryption on notebooks
- Failure to require encryption capabilities
- Not taking BYOD seriously and implementing device-based security policies, such as encryption capabilities

5. Relying Strictly on ISP for Security
It’s not uncommon for companies, especially SMBs to rely solely on their Internet Service Provider (ISP) for security. Not a good idea, considering that this won’t protect you outside of your own network. The same is true if you only protect your network from external threats, and assume that all threats are coming from outside of your organization.
Layered Protection
With the increase in new attack vectors, your protection should be layered to protect against internal, as well as external threats. Layered protection will also help protect your network from attacks via smartphones, external hard drives and USB sticks that can be used to introduce malware to your organization. Your organization should strive to integrate a security infrastructure which includes an internet gateway, web security, email and messaging systems as well as endpoints.
Endpoint Security
Endpoints like PCs, laptops and mobile phones are targets, therefore endpoint security requires each device on a corporate network with comply with certain standards before network access is granted. Endpoint security may include personal firewalls or anti-virus software.
Patch Deployment
Patching is time-consuming but important to protect against malicious attacks on your network. A continuous patching process and an inventory of your assets will help you to prioritize high priority assets first. Forty percent of people don’t upgrade software when prompted and 25 percent need to be prompted twice to do so. This is the perfect example of an easily preventable information security mistake.
80 percent of security breaches are preventable. The costs of implementing technology and processes to secure data are significantly less than the costs of a breach.
Start by talking to your hosting provider and ensure that your company is not making any of the five mistakes listed above. As always, open up the discussion, make sure that you know where your data is hosted and what security measures are in place. Once you talk to your provider, start to implement security best practices internally. A resource plan is also important to have in place in the event that you do suffer a security breach.
Prepare for Information Security Mistakes – Remember These Five Tips
- Have an already established crisis communications plan
- Assign a crisis communications team
- Appoint a crisis communication leader who will liaise with all parties and act as spokesperson
- Identify all key organizational stakeholders; for example: Management, HR, legal counsel, the Board of Directors and Investors.
- Communicate effectively when you are certain of the breach and don’t sugar coat it!
